Key Takeaways
- Compliance is a strategic moat, not just a legal checkbox.
- Map data flows to the correct regulatory framework early in the project.
- Apply the five technical pillars—classification, encryption, access controls, logging, and incident response—throughout the development lifecycle.
- Use the compliance checklist as a living document to ensure evidence for audits.
- Conduct a thorough third‑party vendor risk assessment to protect your supply chain.
- Integrate compliance controls into legacy modernisation to avoid regulatory gaps.
- Regular reviews and transparent evidence keep your software secure and your clients confident.
Introduction
Data security compliance is a foundational requirement for any software solution that handles personal or business information in the UK. While many organisations view it as a legal checkbox, the reality is that a well‑designed compliance program can become a strategic moat, opening doors to regulated markets, shortening sales cycles, and reducing operational risk. This guide walks through the technical and business considerations you need to address when building or modernising software for UK SMEs, with a focus on practical steps you can implement today. FAS Solutions has delivered over 14 years of secure custom software, web, and mobile development, backed by a 95 % data‑security claim and a one‑hour support guarantee. The following sections move from regulatory context to concrete actions, ensuring you finish with a clear, actionable roadmap.
UK Data Security Regulatory Landscape
The UK’s data‑security obligations are layered. At the top sits the General Data Protection Regulation (GDPR), which remains applicable in the UK after Brexit through retained EU law. Complementing GDPR is the UK Data Protection Act 2018, which tailors GDPR to local contexts and adds enforcement powers for the Information Commissioner’s Office (ICO). Beyond these broad privacy rules, the Network and Information Systems (NIS) Regulations impose security requirements on operators of essential services and digital service providers. Industry‑specific rules add further depth: the Financial Conduct Authority (FCA) for financial services, the NHS Digital Security Standard for health‑care providers, and the FCA’s Senior Managers and Certification Regime (SM&CR) for regulated firms.
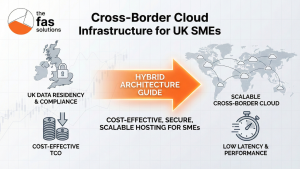
Cross‑border data transfers, especially between the UK and the United States or Australia, require additional safeguards. The UK‑US Data Transfer Agreement and the UK‑Australia Privacy Act framework outline contractual and technical measures such as Standard Contractual Clauses (SCCs) and Binding Corporate Rules (BCRs). For SMEs, the key is to map each data flow to the applicable regulation, document the legal basis, and implement technical controls that satisfy the regulator’s expectations.
Understanding the scope of each rule prevents costly gaps. For example, GDPR focuses on personal data privacy, while NIS targets availability and integrity of critical services. A software platform that processes both customer data and operational telemetry must address both sets of obligations. The following table summarises the primary frameworks and their primary focus:
| Regulation | Primary Focus | Typical Applicants |
|---|---|---|
| GDPR | Personal data privacy, lawful processing | All organisations handling EU‑resident data |
| UK Data Protection Act 2018 | Local privacy enforcement, ICO powers | UK‑based organisations processing personal data |
| NIS Regulations | Security of essential services, incident reporting | Operators of critical infrastructure, digital service providers |
| Sector‑Specific (FCA, NHS) | Industry‑specific security standards | Financial services, health‑care providers |
| Cross‑Border Agreements (UK‑US, UK‑AU) | Legal mechanisms for data transfer | Companies sharing data internationally |
By aligning your project’s data handling model with these frameworks early, you avoid later re‑work and can demonstrate compliance confidently to clients and auditors.
Why Compliance Is a Competitive Moat
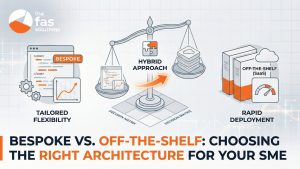
Compliance is often perceived as a cost centre, but for UK SMEs it can be a differentiator that accelerates growth. When a software solution meets or exceeds regulatory expectations, it signals to prospective clients that the provider takes data protection seriously. This trust translates into faster contract negotiations, reduced due‑diligence friction, and the ability to enter markets that demand certified security.
Consider the experience of a UK‑based manufacturing firm that sought to sell its IoT‑enabled equipment to the NHS. The client required evidence of GDPR and NHS Digital compliance before signing. By embedding a compliance‑by‑design architecture, FAS Solutions delivered a solution that passed the NHS’s security audit within weeks, cutting the sales cycle by 30 %.
Beyond trust, compliance reduces operational risk. A breach can trigger ICO fines of up to £17.5 million or 4 % of global turnover, whichever is higher. By adopting a risk‑based approach, you allocate resources where they matter most, lowering the probability of costly incidents.
Finally, compliance opens revenue opportunities. Regulated sectors such as finance, health‑care, and education often have procurement policies that favour vendors with documented security controls and evidence of compliance. Demonstrating a mature compliance program—including data‑classification, encryption, logging, and a proven incident‑response plan—reduces due‑diligence friction and can be a decisive factor in winning bids for regulated‑industry projects.
In summary, robust data security compliance is not a barrier; it is a strategic asset that builds trust, mitigates risk, and expands market access.
Technical Pillars of Secure Software Architecture
A secure software architecture rests on five technical pillars that operate throughout the data lifecycle. Each pillar addresses a distinct risk vector and can be implemented with measurable controls.
- Data Classification – Begin by identifying the sensitivity of each data element. Use a tiered model (Public, Internal, Confidential, Restricted) to guide storage, transmission, and access decisions. Classification drives encryption and logging policies.
- Encryption – Apply encryption both at rest (e.g., AES‑256 on databases and storage) and in transit (TLS 1.2+ for APIs and web traffic). For highly sensitive data, consider end‑to‑end encryption with client‑managed keys.
- Access Controls – Implement role‑based access control (RBAC) and principle of least privilege. Combine authentication (multi‑factor where feasible) with authorisation checks that enforce data‑handling rules.
- Logging and Monitoring – Capture audit trails for data access, modification, and export events. Centralise logs in an immutable store and configure alerts for anomalous patterns. This evidence supports incident response and audit readiness.
- Incident Response and Recovery – Define a documented response plan that includes detection, containment, eradication, and post‑mortem phases. Conduct regular tabletop exercises to validate the plan.
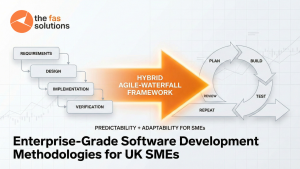
These pillars are not isolated; they intersect. For instance, encryption decisions are informed by data classification, while access controls rely on accurate logging to detect misuse. A practical implementation sequence might look like this:
- Phase 1 – Discovery: Map data flows and classify assets.
- Phase 2 – Design: Choose encryption algorithms, define RBAC roles, and set up logging schemas.
- Phase 3 – Implementation: Apply controls during code development, using automated security testing tools.
- Phase 4 – Validation: Run penetration tests and verify that logs capture required events.
- Phase 5 – Operation: Maintain controls, rotate keys, and review logs weekly.
By embedding these pillars early, you avoid retro‑fitting expensive fixes and build a foundation that scales with your business.
Compliance Checklist for Custom Software Development
The following checklist translates the regulatory landscape and technical pillars into concrete actions for each stage of a software project. Use it as a living document that you update after each milestone.
1. Requirement Gathering
- Identify all data types (personal, financial, operational) and map to applicable regulations.
- Capture legal basis for processing (consent, contract, legitimate interest).
- Define data retention periods and deletion policies.
2. Threat Modelling
- Conduct a STRIDE analysis (Spoofing, Tampering, Repudiation, Information disclosure, Denial of service, Elevation of privilege).
- Prioritise risks based on impact and likelihood.
- Document mitigations in the design specification.
3. Design
- Apply data classification to inform encryption choices.
- Design RBAC matrices aligned with business roles.
- Specify logging requirements (what to log, retention, format).
- Include security controls in the API gateway, database, and front‑end layers.
4. Implementation
- Use secure coding standards (OWASP Top 10) and automated static analysis tools.
- Encrypt data at rest using AES‑256; enforce TLS 1.2+ for all external communications.
- Enforce MFA for privileged accounts and enforce least‑privilege permissions.
- Integrate logging libraries that write to an immutable, time‑stamped store.
5. Testing
- Perform unit and integration tests with security assertions.
- Conduct penetration testing focusing on data flows identified in threat modelling.
- Verify that encryption keys are stored securely and rotated according to policy.
- Validate that audit logs capture required events and are tamper‑evident.
6. Documentation & Evidence
- Create a Data Protection Impact Assessment (DPIA) where required.
- Produce a compliance evidence package (policy documents, technical designs, test reports).
- Maintain a register of third‑party components with their security certifications.
7. Deployment & Operation
- Ensure the production environment meets the same security standards as staging.
- Set up automated monitoring for anomalies in data access patterns.
- Schedule quarterly reviews of compliance controls and update the DPIA as needed.
8. Audit & Continuous Improvement
- Prepare for ICO or sector‑specific audits by organising evidence in a clear folder structure.
- Conduct internal compliance reviews after any major system change.
- Update the checklist based on regulator guidance or new industry standards.
By ticking each item, you create a defensible compliance posture that can be demonstrated to clients, auditors, and regulators.
Third‑Party Vendor Risk Assessment
Supply‑chain security is a critical component of UK data‑security compliance. Many SMEs rely on third‑party libraries, cloud services, or SaaS platforms, each introducing potential vulnerabilities.
Risk Assessment Framework
- Inventory – Maintain a comprehensive list of all third‑party components, including open‑source libraries, APIs, and hosted services.
- Classification – Categorise each component by data sensitivity.
- Due Diligence – Verify the vendor’s security certifications (ISO 27001, SOC 2, GDPR‑compliant contracts). Request a security questionnaire covering encryption, access controls, incident response, and breach‑notification clauses.
- Contractual Safeguards – Include clauses that require the vendor to:
- Provide evidence of security controls.
- Notify you of any breach within a defined timeframe.
- Allow audit access to their security posture.
- Continuous Monitoring – Set up automated alerts for vendor‑reported vulnerabilities (e.g., via CVE feeds) and schedule periodic re‑evaluation.
- Remediation Planning – Define fallback options if a vendor fails to meet required standards (e.g., alternative libraries, migration paths).
Practical Example
A FAS Solutions client used a popular analytics SDK that later disclosed a critical data‑leak vulnerability. Because the vendor had a SOC 2 report and a breach‑notification clause, the client could trigger the clause, receive remediation guidance, and switch to a certified alternative within two weeks, minimising impact.
By institutionalising this process, SMEs can reduce the risk of hidden backdoors and maintain audit‑ready documentation.
Integrating Compliance into Legacy System Modernisation
Modernising legacy systems is a high‑value project, but it also carries compliance risk if data migration is not handled securely. The following steps embed compliance into the migration lifecycle:
1. Data Mapping
- Catalogue all data stores, formats, and locations.
- Identify personal data, financial data, and any data subject to sector‑specific rules.
- Document the legal basis for each data set.
2. Risk‑Based Migration Strategy
- Prioritise data based on sensitivity and business impact.
- Use a phased approach: pilot migration of low‑risk data, then scale to high‑risk assets.
- Apply encryption during transfer (TLS, VPN, or secure file‑transfer protocols).
3. Security Controls in the New Environment
- Replicate the five technical pillars (classification, encryption, access controls, logging, incident response) in the target platform.
- Ensure that any legacy‑to‑cloud APIs meet the same authentication standards.
- Conduct a post‑migration penetration test focused on data‑handling endpoints.
4. Audit Trail Maintenance
- Preserve logs from the legacy system for at least the required retention period.
- Set up a unified log repository that captures both old and new system events.
- Validate that data deletion requests are honoured in the new system.
5. Change Management
- Communicate compliance implications to all stakeholders.
- Train staff on new security procedures (e.g., MFA rollout, data handling policies).
- Update the compliance checklist to reflect migration‑specific items.
By treating migration as a compliance project rather than a purely technical upgrade, you avoid regulatory gaps, maintain client confidence, and reduce the chance of costly re‑work after go‑live.
Conclusion and Next Steps
Data security compliance for UK‑based software solutions is both a legal obligation and a strategic advantage. By understanding the regulatory landscape, embedding core technical pillars, following a detailed checklist, managing vendor risk, and integrating compliance controls into legacy modernisation, you can transform compliance from a cost centre into a competitive moat.
Key actions you can take today:
- Conduct a quick data‑classification exercise for your current projects.
- Review the compliance checklist against upcoming development milestones.
- Initiate a vendor risk assessment for any third‑party components you plan to use.
- Schedule a 30‑minute consultation with FAS Solutions for a free one‑hour support session.
Remember, compliance is an ongoing process. Regular reviews, transparent evidence, and a client‑first mindset will keep your software secure, your clients confident, and your business poised for growth.
Conclusion
Data security compliance for UK‑based software solutions is both a legal obligation and a strategic advantage. By understanding the regulatory landscape, embedding core technical pillars, following a detailed checklist, managing vendor risk, and integrating compliance controls into legacy modernisation, you can transform compliance from a cost centre into a competitive moat. Key actions you can take today include conducting a quick data‑classification exercise, reviewing the compliance checklist against upcoming milestones, initiating a vendor risk assessment for third‑party components, and scheduling a 30‑minute consultation with FAS Solutions for a free one‑hour support session. Regular reviews, transparent evidence, and a client‑first mindset will keep your software secure, your clients confident, and your business poised for growth.
Food for Thought
If your current software lacks a data‑classification model, what first step could you take to introduce one without disrupting operations?
When you encounter a new third‑party library, how do you verify its security posture before integrating it into your codebase?
Consider a recent regulatory update; which part of your compliance checklist would need immediate revision?
If you are preparing for an ICO audit, which documentation items are most likely to be scrutinised and why?
Reflect on a past project where a compliance gap delayed delivery; what lessons can you apply to future initiatives to avoid similar friction?
Frequently Asked Questions
What is the difference between GDPR and the UK Data Protection Act?
GDPR is the EU‑wide regulation that governs the processing of personal data of individuals in the EU. After Brexit, the UK retained GDPR as UK law, but the UK Data Protection Act 2018 adds national provisions, such as enhanced enforcement powers for the Information Commissioner’s Office (ICO) and specific requirements for data‑sharing agreements. Both apply to UK‑based organisations handling personal data, but the Act provides the UK‑specific legal framework and oversight.
Do I need to encrypt all data in my application?
Encryption should be applied to data that is classified as Confidential or Restricted, especially when it is stored at rest or transmitted over networks. Public data may not require encryption, but it is still advisable to protect against tampering. The decision is guided by a risk‑based approach: assess the sensitivity of each data element, the regulatory requirements, and the potential impact of a breach. In practice, encrypt databases, backups, and any API communications that carry personal or financial information.
How often should I review my compliance controls?
Compliance controls should be reviewed at least quarterly, or after any major system change, new regulatory guidance, or significant security incident. A quarterly review ensures that encryption keys are rotated, access permissions are updated, and logging policies remain aligned with business processes. Additionally, conduct a formal audit‑preparation review before any regulator‑mandated audit (e.g., ICO inspection or sector‑specific audit).
What are the key components of a vendor risk assessment?
A vendor risk assessment typically includes: (1) a complete inventory of third‑party components; (2) classification of each component by data sensitivity; (3) verification of the vendor’s security certifications (ISO 27001, SOC 2, GDPR‑compliant contracts); (4) a security questionnaire covering encryption, access controls, incident response, and breach‑notification clauses; (5) contractual safeguards that require evidence of controls, timely breach reporting, and audit rights; and (6) ongoing monitoring through CVE feeds and periodic re‑evaluation.
Can compliance help me enter regulated industries?
Yes. Regulated sectors such as finance, health‑care, and education often require documented security controls and evidence of compliance before awarding contracts. Demonstrating a mature compliance program—including data‑classification, encryption, logging, and a proven incident‑response plan—reduces due‑diligence friction and can be a decisive factor in winning bids for regulated‑industry projects.
What should I do if a security incident occurs?
Immediately activate your incident‑response plan: (1) detect and contain the breach; (2) preserve evidence by isolating affected systems and securing logs; (3) assess impact on personal data and regulatory obligations; (4) notify affected data subjects and the ICO within the statutory timeframes (usually 72 hours for GDPR); (5) remediate vulnerabilities and update controls; (6) conduct a post‑mortem to refine processes and prevent recurrence. FAS Solutions’ one‑hour support guarantee can help you navigate these steps quickly.